|
|

|

|

|

|

|

|
|
|
|

|

|

|
|
|

|
|
|
|
|
|
|
|
|
|
|
|
|

|
 |
|
|
|
|
Mailing List
|
|
By Joining the mailing list you will be notified of site updates.
|
|
Show Your Support For
This Site By Donating:
|
|
|
|
|

|
|
|
|
Audience: Newbies
Last Updated: 10/14/03 1:51 AM
Original Creation Date: 10/14/03 1:51 AM
**All times are EST**
|
|

Telnet
By Erik Rodriguez
This article describes what telnet is and what it is used for.
The telnet service gives users the ability to access a host and perform tasks as if they were working locally. Users
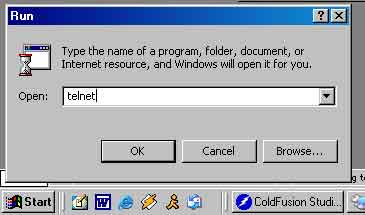
can access a host anywhere in the world using a telnet client. All windows operating systems have a built-in client. You can access telnet by typing "telnet" in the
run box.

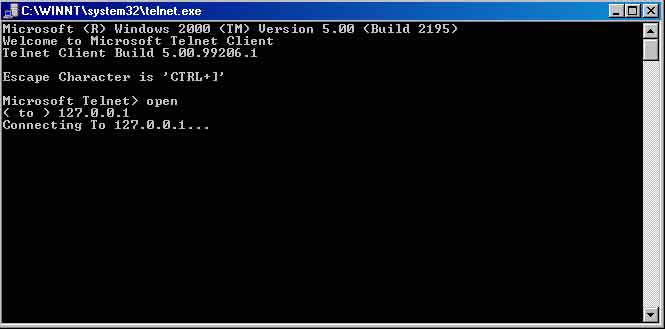
Telnet connects to a host using port 23. It is also used by hackers to gain access to routers, servers, and other network devices. Telnet isn't used as often on
servers now because the communcation between the host and client is not secure. Most network devices still use telnet (routers, switches, and
hubs) but most servers are now using SSH. Telnet can be used to "hop" through multiple devices. See
Telnet Hacking.
|
|
|
|
|
